Existing CSP Client: (919) 424-2060
SALES: (919) 420-3231

Technology has unlocked a world of potential for businesses everywhere. But with these advances comes a new set of problems, like malware. While it’s common knowledge that computers are susceptible to viruses, today’s breed of hackers are more creative than ever. They’re utilizing new, innovative techniques to infiltrate systems of businesses big and small.
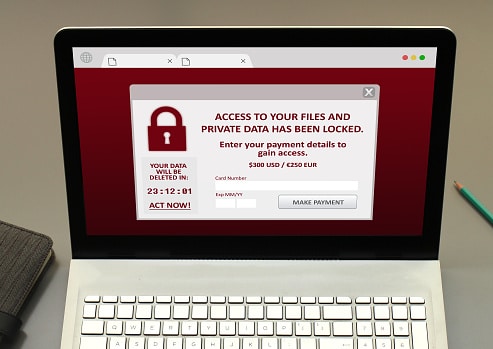
Not all malware is created equal. Just like infectious disease, there are different strains of malware, many with the potential to wreak havoc on your business network. In today’s business landscape, tech departments are faced with the task of not only stopping these attacks before they happen, but with quickly repairing networks in the event that an attack has hit.
The Problem With LoJax
One recent attack has IT departments up in arms. A Russian hacking group created the Rootkit, named “LoJax”. According to ESET, a leader in IT security, the campaign delivering LoJax targeted certain organizations in the Balkans and other countries throughout Central and Eastern Europe.
The problem with LoJax is that it isn’t just any ordinary malware. It’s used to gain persistent access to a computer, and with its reputation for being hard to detect, it’s causing quite the problem for users. Much to the horror of IT professionals, this hacking technique is so complex that it can withstand a variety of common fixes. Some of these include a reformat, a complete OS reinstall and a hard-disk swap.
This unique type of malware lives in a system’s flash RAM, meaning the only way to clear it is to over-write the infected machine’s flash storage. This presents its own set of challenges, and isn’t even a guaranteed fix unless you’re armed with the right code.
What Is Spectre?
Spectre is the name of an underlying vulnerability affecting the vast majority of computer chips manufactured within the last two decades. If this vulnerability is exploited within a system, it could enable attackers to gain access to data that was previously deemed protected. Lojax directly leverages this vulnerability, making it all the more difficult to detect before it hits.
If attackers are successful, they can they utilize LoJax to access systems remotely, and on a constant basis. This allows them to inject it with additional malware. This type of malware can also be utilized to track a particular system’s location, and potentially the owner’s location.
What’s At Risk?
UEFIs are particularly at risk. UEFI, Unified Extensible Firmware Interface, is a specification for the interface between a computer’s operating system and its firmware. It runs pre-boot apps and is responsible for booting the OS. By re-writing the rootkit, the malware is able to stay hidden within the computer’s flash memory, making it difficult to repair.
How To Protect Your Network
Businesses can implement a series of additional security measures to minimize the risk of a cyber attack on their network, especially one as severe and unpredictable as LoJax.
One of the single biggest mistakes businesses are making is running their operations on old, outdated equipment. Not only can this hinder productivity, but it can also leave businesses more susceptible to a cyber attack. Investing in new equipment that runs the latest and most improved hardware means security measures are often built in.
Keeping equipment up-to-date can become costly, but it can also minimize the chances of an even costlier network revamp in the event that a catastrophic cyber attack takes place and compromises everything a company has worked so hard to build.
Exercise Caution With Emails
Malware can gain access to your system through one of several ways. One of the most common methods is e-mail. It’s wise to take a cautionary approach to e-mail when utilizing your work network. Be wary of e-mails from strange e-mail addresses and also be cautious of what websites you are visiting, taking care to only visit safe, reliable sites.
Implement A Secure Boot
While malware like LoJax are especially hard to combat, IT departments can take comfort in the fact that not all hope is lost. One method of prevention is Secure Boot. This mechanism ensures that only securely signed firmware are able to boot up and run on a particular system. With signature verification required, Secure Boot makes it possible to prevent uniquely complex malware like LoJax from successfully infecting a system. Businesses are encouraged to review the Secure Boot configuration throughout the entirety of their hardware.
Malware Cleaning
Once you suspect a computer within your network is infected, it’s important to take action immediately. Be sure to back up your files before you attempt any type of intensive cleaning. Also, don’t attempt to repair complex computer issues alone. Your IT department can help you create a comprehensive game plan to address the problem and prevent similar incidents in the future.
Your system can come under attack when you least expect. Given that phishing is still a go-to strategy for hackers to penetrate systems, security awareness is more important than ever. Create a solid line of defense, and an effective response strategy, to ensure an attack doesn’t compromise your business. Security awareness training can serve an important role in helping your organization stay protected from hackers.

Always at your service to provide the highest level of quality support to our customers.

Anthony Firth Client Engineer

“I’m passionate about building and fostering relationships, and finding solutions for success.”

Michael Koenig Client Account Manager

“I help clients stabilize and grow their IT infrastructure so they can focus on growing their core business.”

Josh Wilshire Systems Engineer Team Lead

“I strive to provide the highest level of quality service to our customers.”

Tommy Williams Sr. Hardware Engineer

“I’m driven by the steadfast belief that technology must serve as a business enabler. This mantra has driven 21
Years of successful partnerships.”

Stephen Riddick VP Sales & Marketing

“CSP doesn’t succeed unless your company succeeds.”

Stephen Allen Inventory Manager

“Through my intuition and genuine concern to help others I have built long-lasting relationships with our customers, co-workers and business partners.”

Scott Forbes VP Support Services

“Every day, I work with clients to help plan the future of their businesses.”

Michael Bowman vCIO

“Your IT problems become our IT solutions.”

Mark McLemore Project Engineer

“Managing internal and external operations to ensure that CSP provides quality and reliable customer service .”

Margie Figueroa Business Manager

“Providing quality internal and externals financial support to our customers and accounting support to CSP.”

Katie Steiglitz Accounting Administrator

“Some call me the CEO. I call myself the Cheerleader for an awesome team!”

William B. Riddick Founder & CEO

“CSP is here to assist you with your IT needs.”

Beth Wylie Inside Sales Manager




On What Questions You Need To Ask Before Signing Any Agreement.
"*" indicates required fields

Raleigh IT Support Company and IT Services Provider | CSP Inc.
1310 Nowell Rd,
Raleigh, NC 27607
Existing CSP Client: (919) 424-2060
SALES: (919) 420-3231
Receive email updates and informative marketing materials by subscribing to our newsletter.
"*" indicates required fields